I am going to do a nmap scan:
| |
We see that we have a ftp server with some images in it.
I downloaded them and tried to upload a file, but it didn’t work out, so I am going to explore the web page.
In the http page there is nothing of interest, but in the https page there is a subdirectory that we can look for:
| |
And we got a message:
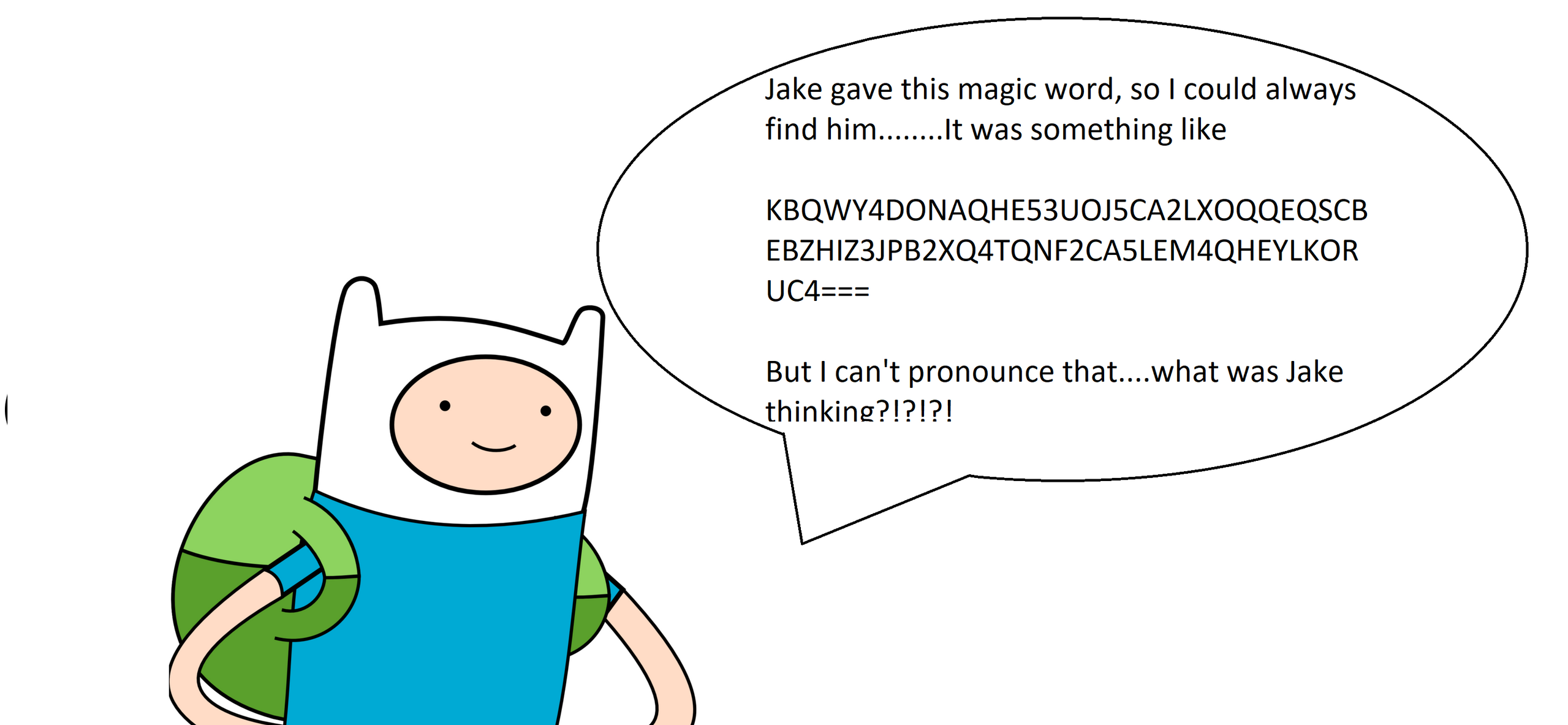
We can decypher with cyberchef:
From there we can find this email address: bubblegum@land-of-ooo.com, which we should put in the hosts file.
Now that we found jake we should re-enumerate the website:
| |
We found another subdirectory
Another time:
| |
And now we got another code:

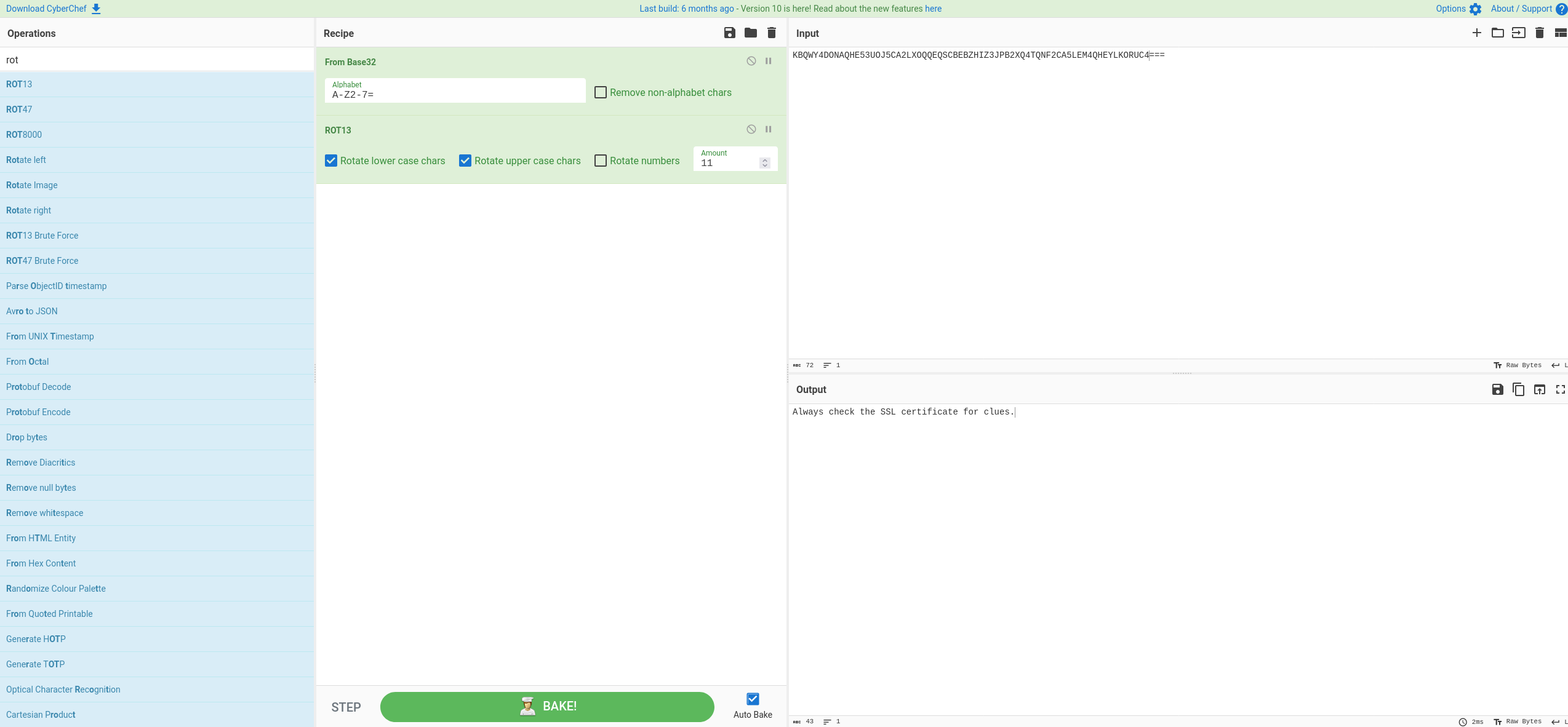
This time we got this:
I tried to put that in the service running but no luck:
| |
So I just started another fuzzer
| |
And finally we got what we were searching:

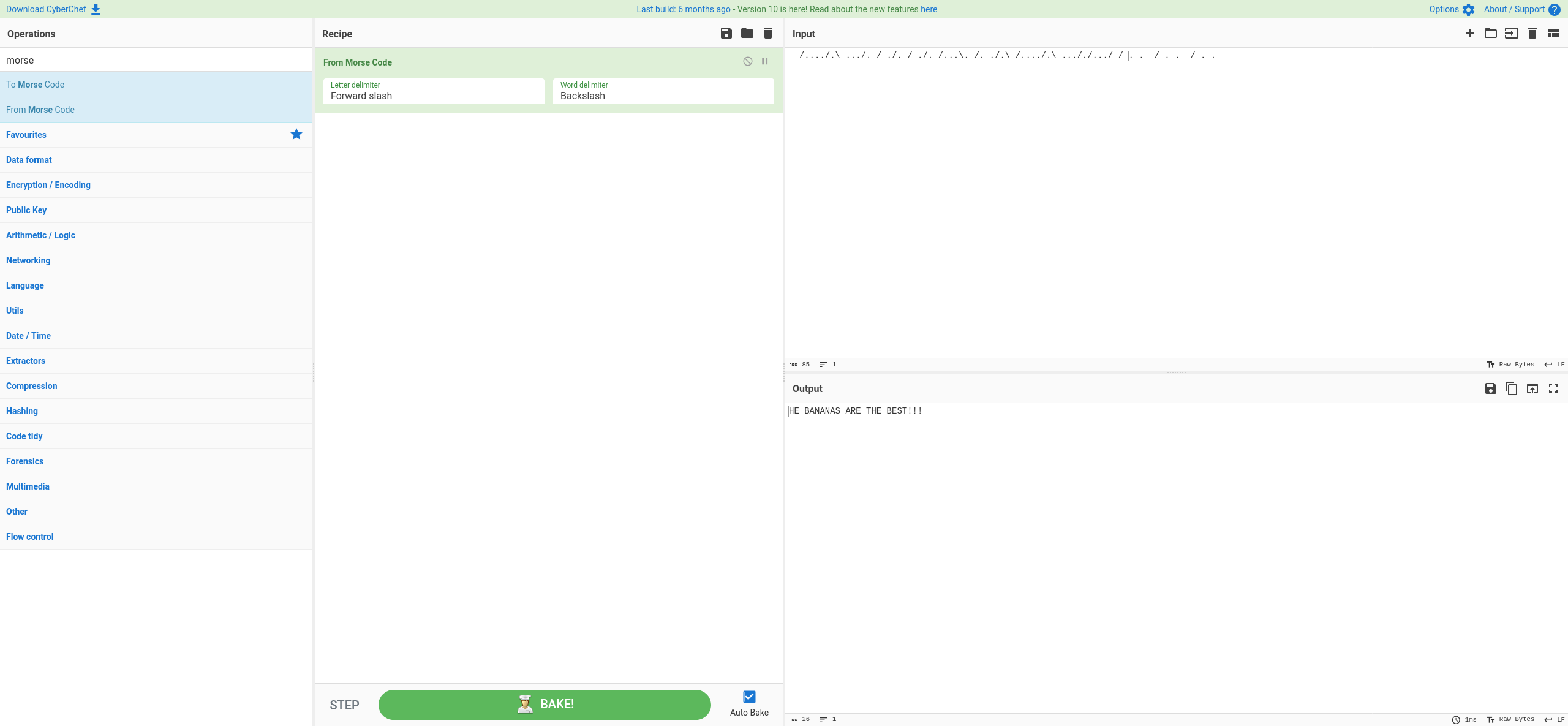
This is either AES or DES,
It was AES.
And we got that:
| |
So I tried using ssh with the password that we found before:
| |
There there are 2 flags, flag1, and flag, the flag one is encrypted in md5.
Since the hint tells us: (Can you search for someones files?)
I searched for the files owned by marceline:
| |
| |
I first tought that was rot13, but after seaching for a while I tried the vigenere one, which requires a key, that in this case would be “gone”
| |
So we got marceline’s password
And we enter ssh with marceline with the password that we just found.
| |
Apparently this is spoon code.
| |
And finally we got the magic word.
Which tells us the peppermint password.
| |
So now we can switch user and retrieve the flag:
| |
We can see a picture in the home directory.
| |
Using “ToKeepASecretSafe” as a password, we are able to find a zip file in the image:
| |
The zip is protected by a password, and we can unzip it using the other password “ThisIsReallySave”:
| |
So now we know that the password starts with The Ice King s and has other 4 characters.
I used https://scrabblewordfinder.org/5-letter-words-starting-with/s to built a text file of possible that I’ll use with hydra.
| |
So, now we can go to the gunter home and retrieve the flag.
Now I am going to search for root SUIDs:
| |
Exim is a strange file.
| |
I found this exploit: https://raw.githubusercontent.com/AzizMea/CVE-2019-10149-privilege-escalation/master/wizard.py
we can copy the script, change the port to the one that exim4 is running and execute it.
| |
So now we just want to find the last flag, which is in the bubblegum home.
| |